What is PAM and why do we need it?
What is PAM and why do we need it?
Security incidents, breaches, and threats are inevitable in today's technology-driven world. The real question is not if they will happen, but when. This is why it's crucial to implement strategies and technologies that prevent, contain, mitigate, and remediate such incidents. When talking about security, there are different strategies and technologies used to prevent, contain, mitigate, and remediate threats to endpoints. This includes physical and virtual devices that connect to a corporate environment. Compromised endpoints can give attackers a foothold within an environment and enable them to launch further attacks.
In fact Check Point Research (CPR) has reported...
a 50% increase in attacks on corporate networks in 2021, many of which involve exploiting privileged credentials. According to the Verizon Data Breach Investigation 2022 report, 67-72% of data leaks involve privileged credentials, which also result in a higher cost of up to $4.37 million.
A survey by Sapio Research reveals that 84% of organizations experienced an identity-related breach or an attack using stolen credentials. With the increasing use of technology, cyber threats are expected to further intensify. One solution to minimize these risks is investing in PAM, which applies the least privilege principle to ensure users have only the necessary permissions to perform their activities.
Privileged Access Management (PAM)
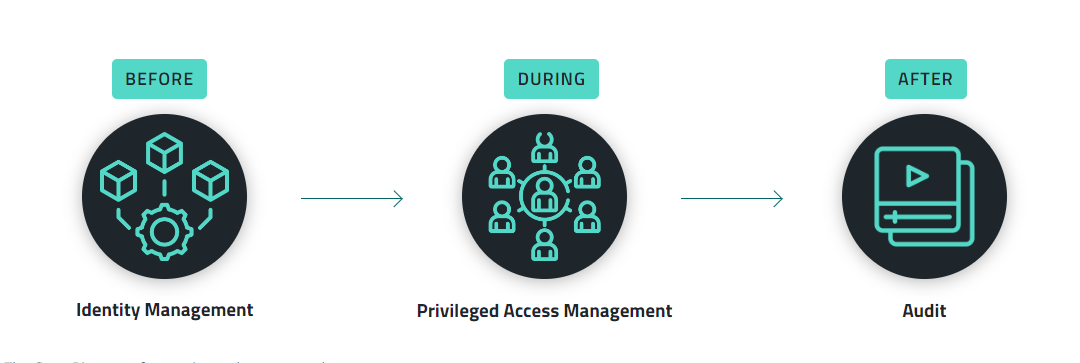
PAM is a set of technologies and practices that aim to control, monitor, and audit access to privileged accounts and sensitive resources within an organization's IT environment. The purpose of PAM is to reduce the risk of data breaches and cyberattacks that can result from unauthorized access to critical systems and information by privileged users, such as system administrators, network engineers, and database administrators. By separating users from privileged rights and granting rights only in situations where users have the right to perform specific activities, PAM ensures better security for the organization. Additionally, PAM allows organizations to monitor and record all activities performed during privileged sessions, helping to protect against insider threats and data theft.
Any credential that has broad rights, which include accessing relevant data, changing, removing, or deleting files and programs, and having access to systems, is considered a credential with privileged access.
Senhasegura 360º
Senhasegura 360º Privilege Platform is designed to protect against cyber-attacks that use privileged credentials and data leaks and offers secure storage, segregation of access, and full traceability of use, providing compliance with data protection legislation. Through intuitive interface you can maintain an audit trail and session logs for all administrative credential usage, enhancing user traceability and facilitating auditing. As a solution it helps you ensure secure access to sensitive information, protect critical environments, and detect suspicious activity to prevent data theft.
It also helps to increase the level of security related to privilege elevation, reduce the number of accounts with elevated access and control the access to the devices. It allows you to monitor and record all activities performed during privileged sessions and helps you protect your business from insider threats and data theft.
Summary
Senhasegura has received numerous awards and recognition, including being ranked number one for customer satisfaction by Gartner.

Senhasegura's 360º Privilege Platform has been honored with three Cybersecurity Excellence Awards for its exceptional performance in Privileged Access Management (PAM), Certificate Lifecycle Management and Cloud Privileged Access Management. These accolades are based on the feedback of nearly 600,000 cybersecurity professionals and recognize the platform's capability to secure and control privileged and generic credentials, prevent cyberattacks and data leaks, and help companies achieve compliance with regulatory standards such as PCI, ISO, SOX, and GDPR.
Senhasegura as a PAM solution increases security related to privilege elevation, reduces the number of elevated access accounts, and controls device access. It offers a centralized audit data repository, synchronizes password changes with the database, and provides updated passwords to embedded applications via its API, while also allowing for easy removal of encrypted passwords and credentials from data sources.
Sources:
Check Point Research - CPR
Verizon Data Breach Investigation 2022 - https://www.verizon.com/business/resources/reports/dbir/
Sapio Research - https://senhasegura.com/gartner-iam-summit-why-you-should-consider-attending/
Awards:
19th Annual 2023 Globee® Cybersecurity Awards winners
2023 Cybersecurity Product / Service Awards – Winners
Gartner Peer Insights
Senhasegura - Testimonials


