Why Your M365 Backup Isn't Enough Anymore
Why Your M365 Backup Isn't Enough Anymore
In today’s landscape, attackers don't "hack" systems; they log in using your own identities. Identity is the new perimeter, and traditional security solutions are blind to this. Modern threats like Evilginx bypass MFA by hijacking session tokens, while Consent Phishing uses malicious OAuth apps to gain permanent, passwordless access to your data. Once inside, they use “Stealth” tactics like hiding mailbox rules to intercept invoices or silently exfiltrating OneDrive files.
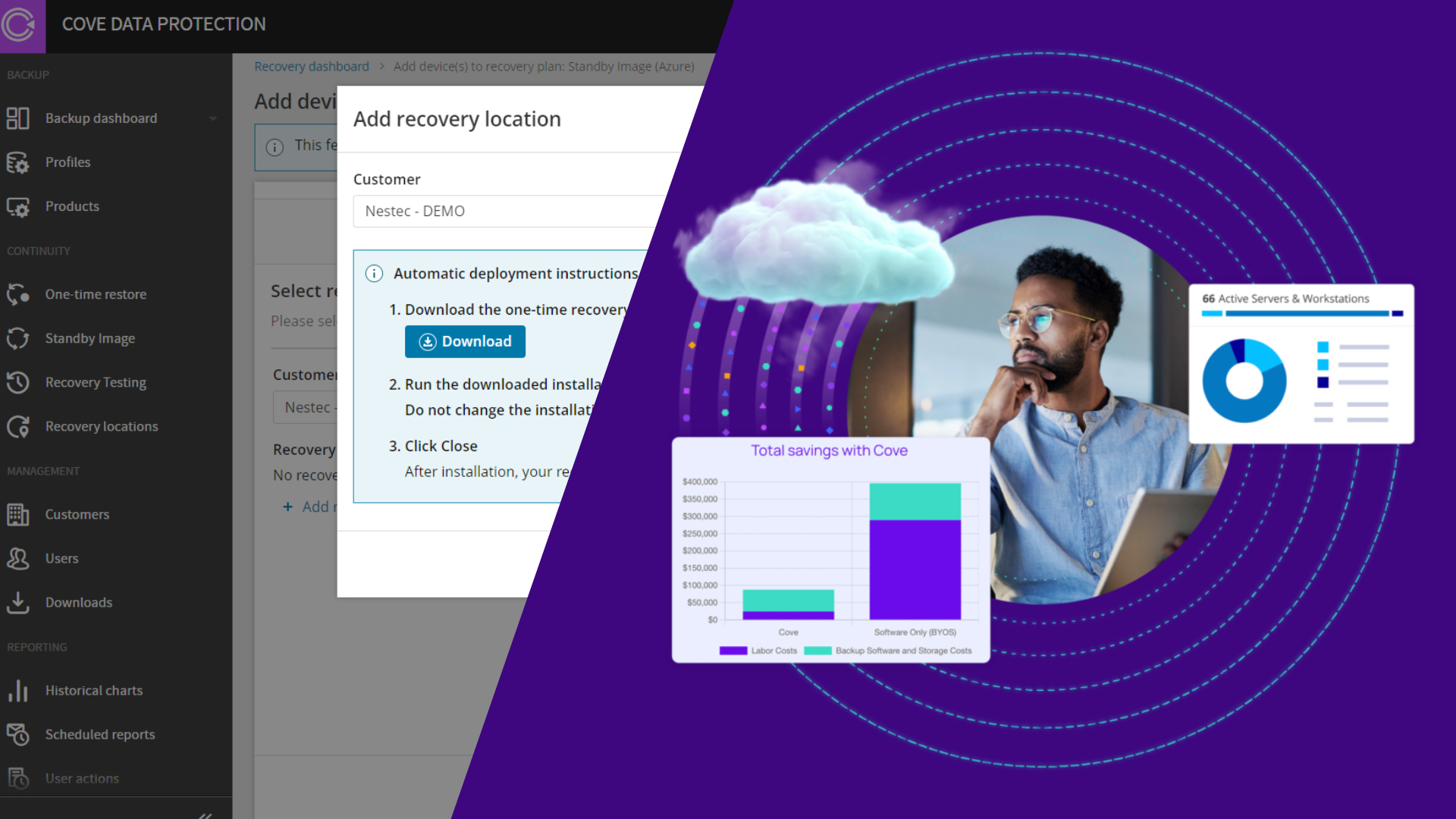
Cove and ITDR winning combination
N-able ITDR (Identity Threat Detection and Response) combined with Cove Data Protection closes this gap. ITDR acts as the "Kill Switch," using behavioral analytics to detect "Impossible Travel" or session theft. It doesn't just alert; it automatically Revokes Sessions and disables accounts to neutralize attackers in seconds. Cove then serves as the "Truth Filter" allowing you to compare current settings against clean backups to instantly wipe hidden rules and restore integrity. Cove Data Protection provides an out-of-band "Time Machine" to revert malicious settings and restore data.
How ITDR catches Evilginx aka "Session Theft" Alerts
Evilginx steals the session token (cookie), so the login looks "valid." ITDR catches this by noticing that the token is being used by a different person or machine than the one that created it.
Specific Alert Names to Automate:
-
"ASN Deviation Detected": This is the silver bullet for Evilginx. If a session started on a regular ISP IP (home), but 10 minutes later is performing actions from a foreign IP (Attacker's proxy server), ITDR flags the Autonomous System Number (ASN) change.
-
"Impossible Travel": If a token is used in Berlin and then 20 minutes later in Zagreb, the session is hijacked.
-
"Unusual Browser/User-Agent Change": Flags when a session cookie issued to Chrome/Windows is suddenly used by a Python script or a different browser mid-session.
The Opportunity Cost of Manual Response
The greatest risk in 2026 is the "human gap”. If you rely on manual alerts, you are trading hours of data loss for a few minutes of convenience. Every minute an attacker spends inside a trusted session is a minute they use to establish persistence that a password reset won’t fix.
The opportunity cost of manual response is your entire tenant's integrity, and by the time a human sees the alert, the invoice has been redirected, and the backups have been targeted. Automation isn't just a feature; it is the only way to move at the speed of the threat.
Conclusion
True cyber resilience requires moving beyond simple "prevent and restore." By integrating N-able ITDR's with Cove’s granular recovery, you create a defensive loop that identifies, punishes, and repairs identity-based attacks. In a world where credentials are stolen daily, your survival depends on how fast you can turn a trusted identity back into a locked gate.