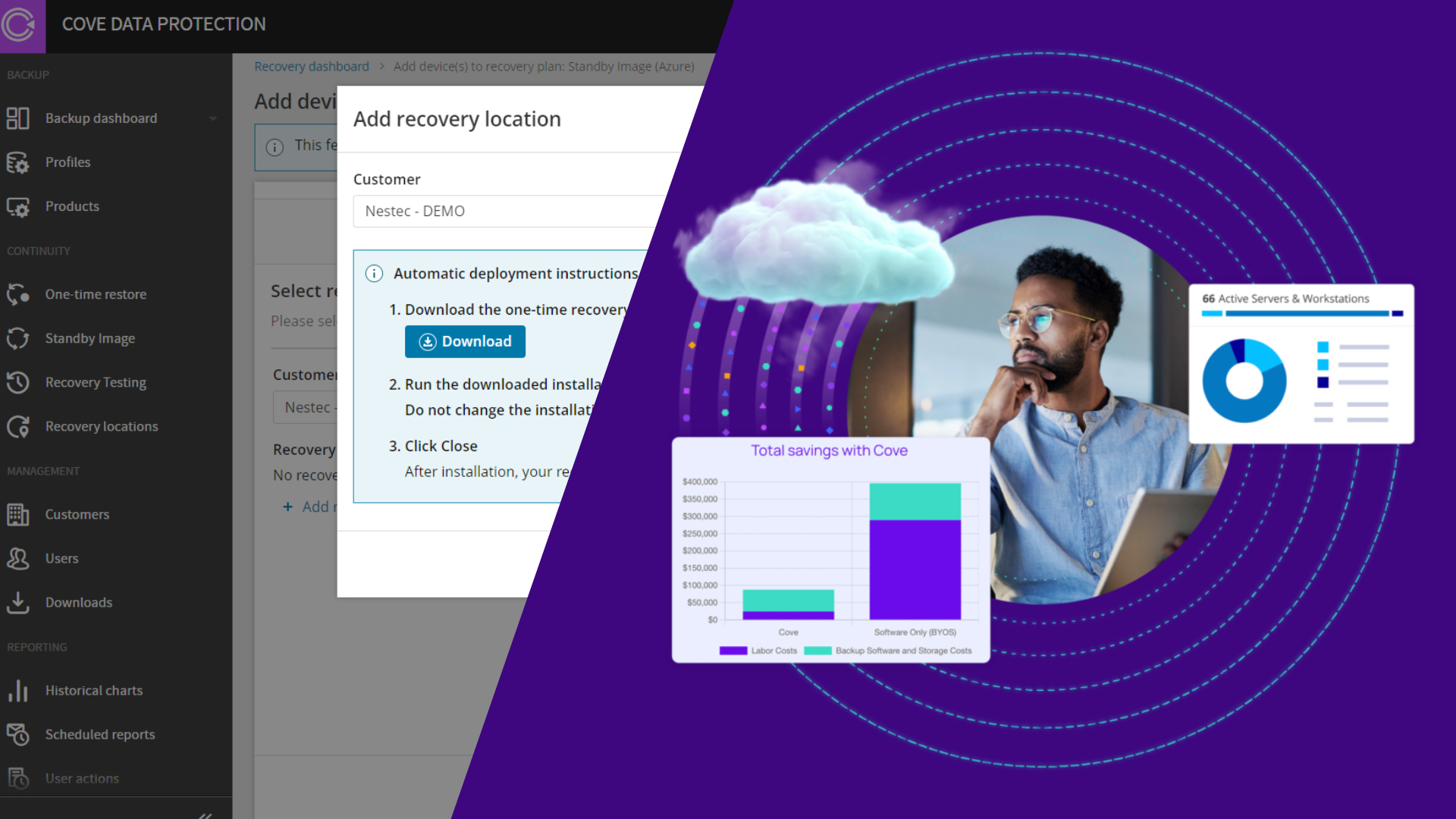
Cloud secrets and AI keys at risk
According to a recent Sentinel One report, AI adoption has become the primary driver of cloud risk, with AI specific credential exposure increasing by 140% and “Shadow AI” creating unmonitored attack surfaces. Attackers are exploiting legacy vulnerabilities to gain access and utilizing exposed API keys to manipulate AI models, prompting a need for continuous surface monitoring and automated secrets management.